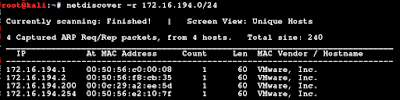
This is writeup for Vulnhub machine: Lazysysadmin Machine can be download from here: https://www.vulnhub.com/entry/lazysysadmin-1,205/ Target IP is 172.16.194.199 Next, run nmap scan: Found port 22, 80, 139, 445, 3306, 6667 I start with http scan Found wordpress and phpmyadmin, looks really interesting! Try to dig more with wpsccan and see the site: There is "My name is togie", this looks interesting, maybe the system's username or something else Run wpscan: Try some default credentials on wordpress login, but not work... After I cannot dig anything, I try to turn into samba service: Next, try to access the server with smbclient: Great! We can access without any password. And we have file name deets.txt, open on browser and got: Try again on wordpress, but not work. Next file is default password file wp-config.php After get the file, open it and ...